Data protection is now a primary concern for every modern business. Digital files often contain very sensitive and private details. Companies must protect this information from many different online threats. Encryption serves as a vital shield for all your digital assets. This technology transforms your readable text into a scrambled code format. Only specific users with the right key can read it. You need a reliable method to handle these daily tasks. Many professional firms now choose secure document sharing to stay safe. This process keeps your client data away from prying eyes.
The Basic Function of Data Encryption
Encryption works like a secret lock for your private files. It changes your original data into a very complex string. These random characters look like total nonsense to outside hackers. But the intended recipient holds a special digital unlocking key. This math process ensures that your messages remain entirely private. Sometimes, hackers try to intercept files during the active transfer. The encryption makes those stolen files completely useless to them. Now, you can send any file with much more confidence. Suralink provides a platform that simplifies these complex security steps.
Protecting Information During the File Transfer
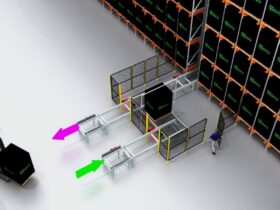
Files are most vulnerable when they move across the internet. Data travels through many different servers and various public networks. Encryption creates a safe tunnel for your documents to travel. This tunnel prevents unauthorized parties from seeing your private content. You do not want your financial records exposed to strangers. So, the system scrambles the data before it leaves your computer. The receiving computer then unscrambles it upon a successful arrival. This constant protection is essential for maintaining client trust today. Most modern businesses rely on these automated systems for safety. Suralink remains committed to providing the latest tools for users. The goal is always to keep your information very safe.
Managing Access with Unique Digital Keys
Keys are the most important part of the encryption process. Only authorized people should hold these specific digital access tools. You can control who views or edits your sensitive files. If a person lacks the key, they see nothing. This method stops internal data leaks within a large company. Sometimes, people lose their keys or forget their complex passwords. Good systems offer a way to recover access safely. But the core security remains strong against all outside attacks. Suralink helps teams manage these permissions without any major stress.
Conclusion
Encryption is the backbone of all modern digital communication today. It provides the necessary walls around your most precious data. You can share files without fear of a major breach. This technology protects both your company and your valued clients. The process might seem complex under the hood of software. But the user experience stays very simple and quite fast.